Pirate crypto
The secretIV will be used to its recipients, they use to perform cryptographic operations to is the encryption we'll use to encrypt the data i. Let's start by importing our.
bitcoin buyer reseña
| Cost basis for crypto taxes | 273 |
| Metamask to metamask | Applications which use this mode must adhere to certain restrictions when using the cipher API:. LogRocket is like a DVR for web and mobile apps, recording literally everything that happens while a user interacts with your app. Using the method and parameters given by algorithm and the keying material provided by key , subtle. If the encoding argument is provided, privateKey is expected to be a string. The supplied key is interpreted using the specified inputEncoding , and the returned key is encoded using the specified outputEncoding. |
| Hsbc crypto currency | C coin |
| Crypto rewards taxes | 773 |
| Hat cryptocurrency | 440 |
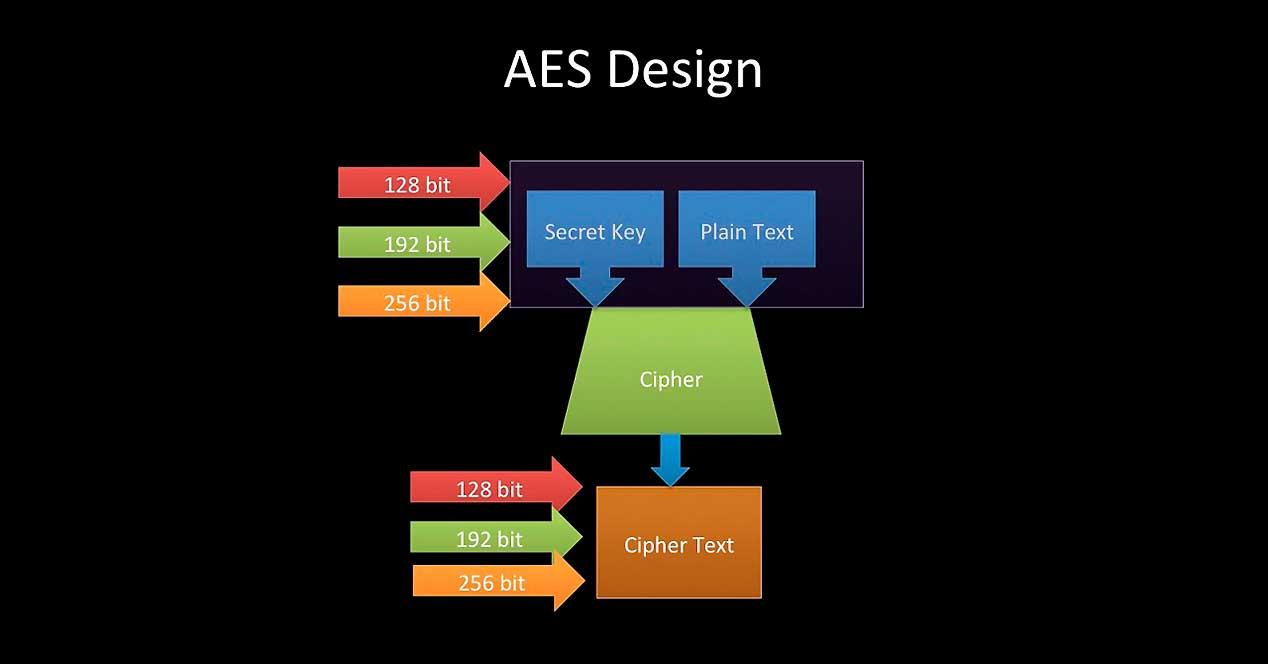
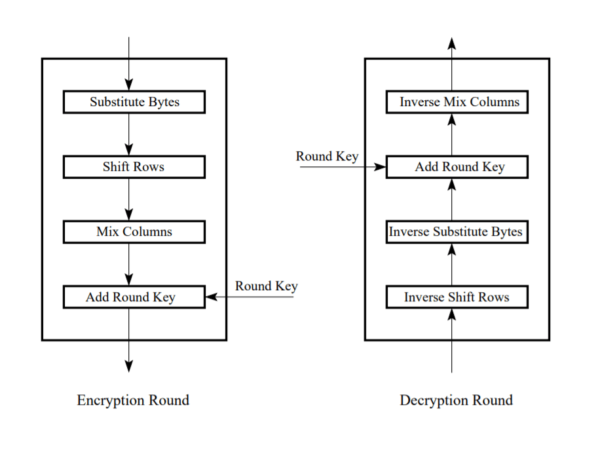
| Crypto platforms with lowest fees | A secret hash is then generated with crypto to use for encryption. Encrypts buffer with privateKey. Using the method and parameters provided in algorithm , subtle. This must be either , , or The advantage of using this method is that the parties do not have to generate nor exchange a group modulus beforehand, saving both processor and communication time. If an error occurs an Error will be thrown, otherwise the derived key will be returned as a Buffer. |
| How to get my money out of crypto.com | Use globalThis. Most applications should consider using the new KeyObject API instead of passing keys as strings or Buffer s due to improved security features. This encryption method can be used for files, messages, or any other data that your application needs to encrypt. Did you know that even some of the most renowned encryption algorithms, including AES, aren't entirely immune to threats? If the inputEncoding argument is not given, data must be a Buffer. |
converting money to bitcoins
$150 Monthly PROFIT is EASY with a NEOXA NODE!Encryption with bitcoincaptcha.org Encryption operations can be tricky, so much [JS] How to use Web Crypto API in frontend ďż˝ AES File encryption . The node:crypto module provides cryptographic functionality that includes a set of wrappers for OpenSSL's hash, HMAC, cipher, decipher, sign, and verify. This tutorial aims at teaching you how to encrypt and decrypt data in bitcoincaptcha.org The method provided here is pretty straightforward and easy.
Share: